Whilst KNX IP Secure and KNX Data Secure protect KNX installations from unauthorised local or remote access, Christian Kiefel reminds us that we must also consider the security of cloud-based voice assistants connected to systems within the home.
The market for voice-controlled assistants is rapidly expanding worldwide, and is expected to grow by 7% per annum over the next three years. This is, in part, due to the end-user’s ease of access in the form of low-cost home speakers, or as a pre-embedded smartphone feature.

The adoption of personal voice assistants such as Alexa and Google Assistant are a key factor behind smart home growth, however all of these solutions are based on a cloud-centric approach where data is collected and processed on an external computer infrastructure. This reliance on the cloud brings serious user privacy issues into play, and also opens the gates to malicious actors, who are capable of attacking these systems in various ways, ranging from illicit data collection to attacks on the devices themselves to carry out damaging commands.
Access by skills
Security against attacks from the Internet depends, among other things, on the system structure. Today, KNX IP Secure and KNX Data Secure ensure that unauthorised access to the KNX installation is impossible, even if the network or bus cable is accessible.
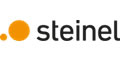
However, when using a voice assistant such as Amazon’s Alexa, so-called ‘skills’ must be activated for various tasks. More than 100,000 of these skills, developed by companies all over the world, are already available. Depending on the application, each skill opens access to the in-house intranet, to various devices installed in the house, and to the KNX installation if it is deemed necessary. This access is required so that the voice commands are able to operate and query the devices. The access must be kept permanently open so that a voice command can be executed at any time.
Who is responsible?
Access and access data are the responsibility of the skill provider and not Amazon.
“When people use Alexa to play games or seek information, they often think they’re interacting only with Amazon,” says Anupam Das, assistant professor of computer science at North Carolina State University. “But a lot of the applications they are interacting with were created by third parties, and we’ve identified several flaws in the current vetting process that could allow those third parties to gain access to users’ personal or private information.” [1]
The manufacturer of the Alexa gateway installed in the house also has access to the in-house intranet, and to the KNX installation via the skill when needed. In addition to recordings made by the online voice assistants previously mentioned in this article, this channel creates an increased risk of attack from the Internet.
Figuratively speaking, the front door for installation is secured at the highest level by KNX, but with each activated skill, the owner gives the key to this door to strangers.
Additionally, the homeowner becomes dependent on the device manufacturer of the third-party gateway. They trust that the service, which is generally offered free of charge, will be maintained in the long term. It should be noted that this service is associated with running costs for the manufacturer, therefore a functional guarantee that is not limited in time, must be questioned.
Due to this, it is highly recommended that the trustworthiness of the developer or the device manufacturer needs to be examined before activating a skill. In addition, the terms of GDPR (DSGVO) consent should be carefully read.
Other recommendations to increase protection
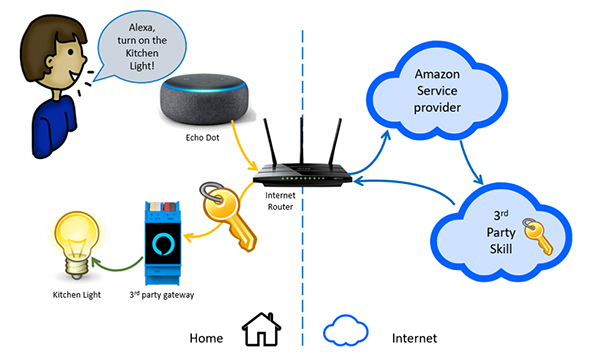
Alternatively, an option to consider is an offline voice assistant that is used specifically for operating a KNX installation, such as the Aragon smart speaker by ProKNX. No skills are required, no Internet portal has to be activated, and no access data has to be given away. Access to the KNX installation is carried out by the local Intranet through secure https commands, so there is no possibility of intrusion.
Conclusion
Along with the installation of KNX IP Secure and KNX Data Secure to protect data from malicious attacks or harvests, a smart speaker that works completely offline is a valid alternative to generic cloud-centric assistants when installing a smart system. In the future, these options will become essential as protecting the security of users
becomes a highly-requested feature of a smart system.
References
[1] Feb. 21-24, Network and Distributed Systems Security Symposium 2021, North Carolina State University (https://news.ncsu.edu/2021/03/alexa-skill-vulnerabilities/), (https://anupamdas.org/paper/NDSS2021.pdf)
Christian Kiefel is the CEO of ProKNX, an innovative French company in the KNX home automation sector that makes offline smart speakers.